Table of Contents
- Introduction: When Access Becomes the Bottleneck
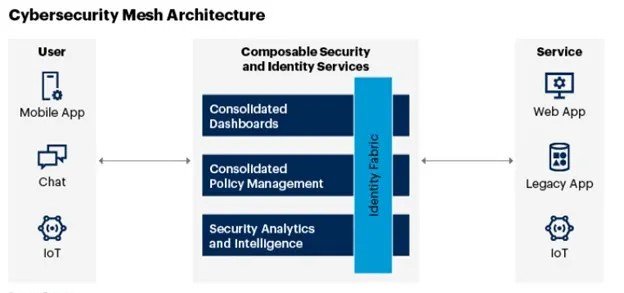
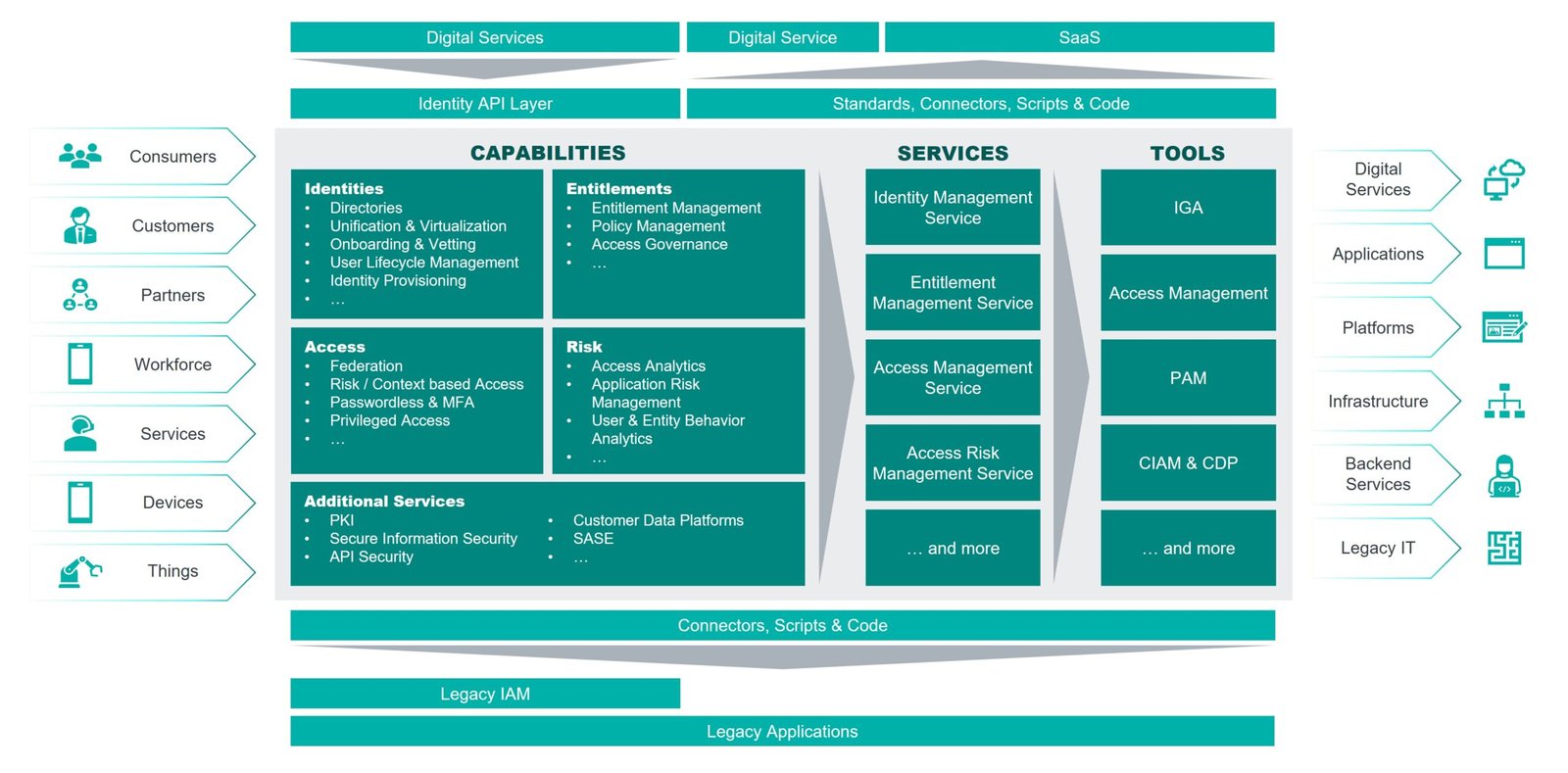
- What Is Identity Fabric Architecture?
- Why Traditional Identity Models Break Down
- The Core Principles of Identity Fabric Architecture
- Key Components of an Identity Fabric
- Practical Use Cases in B2B Enterprises
- Mini Case Example: Simplifying Access in a Complex Environment
- How to Implement Identity Fabric Architecture
- Common Mistakes to Avoid
- A Contrarian Take: Identity Is Not Just a Security Problem
- Quick Checklist: Are You Ready for Identity Fabric?
- The Future of Identity in Enterprises
- Conclusion: From Fragmentation to Control
Introduction: When Access Becomes the Bottleneck
If you’re leading IT, security, or digital transformation in a large enterprise, you’ve likely run into this problem.
Your organization has grown fast. New cloud platforms, SaaS tools, remote teams, partners, and acquisitions have all added layers to your environment. Each system has its own way of managing identities and access.
What you end up with is:
- Multiple identity stores
- Inconsistent authentication methods
- Fragmented access policies
- Poor visibility into who has access to what
Then comes the inevitable question from leadership or auditors:
“Can we confidently say the right people have the right access at the right time?”
For many enterprises, the honest answer is no.
This is exactly the challenge that Identity Fabric Architecture is designed to solve.
In this article, we’ll break down what identity fabric really means, why traditional identity models fall short, and how to build a unified approach that scales with your business.
What Is Identity Fabric Architecture?
Identity Fabric Architecture is a modern approach to identity and access management that connects and orchestrates identity services across systems, environments, and users through a unified layer.
Instead of replacing existing systems, it integrates them.
A Simple Way to Understand It
Think of identity fabric as a connective layer that:
- Links identity sources
- Standardizes access policies
- Enables consistent authentication
- Provides centralized visibility
Across:
- Cloud and on-prem systems
- Employees, partners, and customers
- Applications, APIs, and data
Why Traditional Identity Models Break Down
Most enterprises did not design their identity systems from scratch. They evolved over time.
1. Identity Silos
Different systems manage identities separately:
- Active Directory for employees
- SaaS apps with their own login systems
- Customer identity platforms
- Legacy applications with custom authentication
These silos create:
- Duplication
- Inconsistency
- Security gaps
2. Inflexible Architectures
Traditional identity systems are often rigid.
They struggle to support:
- Multi-cloud environments
- Hybrid workforces
- External collaborators
- Rapid application deployment
3. Poor User Experience
Users face:
- Multiple logins
- Complex authentication flows
- Delays in access provisioning
This impacts productivity and adoption.
4. Limited Visibility
Security teams often lack a unified view of:
- Access permissions
- Identity activity
- Risk signals
Without visibility, governance becomes reactive.
The Core Principles of Identity Fabric Architecture
To understand how identity fabric solves these problems, let’s look at its foundational principles.
1. Integration Over Replacement
Identity fabric does not require ripping out existing systems.
Instead, it:
- Connects identity providers
- Bridges legacy and modern systems
- Enables interoperability
This reduces disruption and speeds up adoption.
2. Centralized Policy, Distributed Enforcement
Policies are defined centrally but enforced across systems.
This ensures:
- Consistency
- Flexibility
- Scalability
3. Context-Aware Access
Access decisions are based on context, such as:
- User role
- Device type
- Location
- Behavior patterns
This enables adaptive security.
4. Continuous Identity Validation
Identity is not verified once at login. It is continuously assessed.
This aligns with zero trust principles.
5. Unified Visibility and Analytics
All identity-related data flows into a central layer for:
- Monitoring
- Reporting
- Risk analysis
Key Components of an Identity Fabric
Let’s break down what typically makes up this architecture.
Identity Providers and Directories
These are your existing systems:
- Enterprise directories
- Cloud identity platforms
- Customer identity systems
The fabric connects them.
Access Management Layer
Handles:
- Authentication
- Authorization
- Single sign-on
- Multi-factor authentication
Identity Governance
Manages:
- Access policies
- Role definitions
- Access reviews
- Compliance requirements
API and Integration Layer
This is critical.
It enables:
- Communication between systems
- Integration with applications
- Real-time data exchange
Analytics and Intelligence
Provides:
- Risk scoring
- Behavior analysis
- Insights into access patterns
Practical Use Cases in B2B Enterprises
Let’s move from theory to application.
1. Unifying Employee Access Across Tools
A large enterprise uses:
- Multiple SaaS platforms
- On-prem applications
- Cloud infrastructure
With identity fabric:
- Employees get a single, consistent login experience
- Access policies are applied uniformly
- IT gains visibility into usage and permissions
2. Managing Partner and Vendor Access
External users often create risk.
Identity fabric enables:
- Controlled access provisioning
- Time-bound permissions
- Continuous monitoring
3. Supporting Mergers and Acquisitions
M&A introduces identity complexity.
Instead of merging systems immediately, identity fabric:
- Connects different identity environments
- Maintains security and access control
- Enables gradual integration
4. Enabling Zero Trust Security
Identity fabric is a key enabler of zero trust.
It supports:
- Continuous authentication
- Context-based access decisions
- Least privilege enforcement
Mini Case Example: Simplifying Access in a Complex Environment
A global tech company struggled with:
- Multiple identity systems
- Inconsistent access policies
- High support tickets for login issues
They implemented an identity fabric approach:
- Integrated existing identity providers
- Centralized access policies
- Introduced adaptive authentication
Results
- Reduced login friction for users
- Improved security posture
- Lowered IT support workload
- Faster onboarding for new employees
The biggest win was consistency across the organization.
How to Implement Identity Fabric Architecture
You don’t need a complete overhaul to get started.
Step 1: Assess Your Identity Landscape
Map:
- Identity sources
- Applications
- Access flows
- Current pain points
Step 2: Define Your Goals
Focus on outcomes like:
- Improved user experience
- Stronger security
- Better visibility
- Faster provisioning
Step 3: Choose Integration Points
Identify where to connect systems first.
Start with high-impact areas such as:
- Core business applications
- High-risk systems
Step 4: Centralize Policies
Define:
- Access rules
- Authentication requirements
- Role-based controls
Step 5: Enable Context-Aware Access
Incorporate signals like:
- Device health
- Location
- Behavior
Step 6: Build Visibility
Create dashboards for:
- Access activity
- Risk insights
- Compliance tracking
Step 7: Iterate and Expand
Identity fabric is not a one-time project.
Expand coverage over time.
Common Mistakes to Avoid
1. Trying to Replace Everything
This leads to:
- High costs
- Long timelines
- Operational risk
Focus on integration instead.
2. Ignoring User Experience
Security without usability will fail.
Balance both.
3. Lack of Governance
Without clear policies, the system becomes inconsistent.
4. Underestimating Integration Complexity
Plan carefully for:
- Legacy systems
- APIs
- Data synchronization
A Contrarian Take: Identity Is Not Just a Security Problem
Most organizations treat identity as a security function.
That’s too narrow.
Identity impacts:
- User experience
- Productivity
- Customer engagement
- Business agility
Identity fabric should be seen as a business enabler, not just a security layer.
Quick Checklist: Are You Ready for Identity Fabric?
- Do you have multiple identity systems that don’t integrate well?
- Are access policies inconsistent across applications?
- Do users struggle with multiple logins?
- Is visibility into access limited?
- Are onboarding and offboarding processes slow?
If yes, identity fabric can deliver immediate value.
The Future of Identity in Enterprises
As enterprises become more distributed, identity will be the core control layer.
Expect to see:
- More decentralized identity models
- AI-driven access decisions
- Deeper integration across ecosystems
- Stronger alignment with zero trust frameworks
Identity fabric will be central to this evolution.
Conclusion: From Fragmentation to Control
Identity is no longer just about logging in. It is about controlling access in a complex, dynamic environment.
Identity Fabric Architecture provides a way to:
- Unify fragmented systems
- Simplify user experiences
- Strengthen security
- Enable business agility
Start by connecting what you already have. Build a unified layer. Focus on visibility and consistency.
Because in modern enterprises, the organizations that manage identity well are the ones that move faster, stay secure, and scale with confidence.




Leave a Reply