Table of Contents
- Introduction: Why Risk Feels Out of Control
- What Is IT Risk Posture Management?
- Why Traditional Risk Management Models Are Failing
- The Shift: From Risk Management to Risk Posture Management
- The Unified Model for IT Risk Posture Management
- Mini Case Example: From Chaos to Clarity
- Practical Framework: How to Get Started
- Common Mistakes to Avoid
- A Contrarian Take: More Data Is Not the Answer
- Quick Checklist: Is Your Risk Posture Management Effective?
- The Future of IT Risk Posture Management
- Conclusion: From Visibility to Control
Introduction: Why Risk Feels Out of Control
If you’re responsible for security, IT, or compliance in a modern enterprise, the pressure is familiar.
New tools get added every quarter. Cloud environments expand. Teams adopt SaaS without always informing IT. Meanwhile, threats evolve faster than policies can keep up.
You might have:
- A vulnerability scanner running weekly
- A compliance dashboard tracking frameworks
- Security alerts flowing into a SIEM
- Spreadsheets attempting to tie everything together
Yet when leadership asks a simple question, things get uncomfortable:
“What is our current risk posture?”
Most organizations can’t answer this clearly. Not because they lack data, but because their data is fragmented.
This is where IT Risk Posture Management comes in.
In this article, we’ll break down what it really means, why traditional approaches fall short, and how to build a unified model that gives you clarity, control, and confidence in your risk decisions.
What Is IT Risk Posture Management?
At its core, IT Risk Posture Management is the practice of continuously understanding, assessing, and improving your organization’s overall risk exposure across systems, data, and operations.
It answers questions like:
- Where are we most vulnerable right now?
- Which risks matter the most to the business?
- Are we improving or getting worse over time?
- What should we fix first?
Beyond Point-in-Time Risk Assessments
Traditional risk assessments are static. They happen quarterly or annually.
Modern environments are dynamic.
- New assets are created daily
- Configurations change constantly
- Threats evolve in real time
IT Risk Posture Management shifts from snapshot thinking to continuous visibility.
Why Traditional Risk Management Models Are Failing
Before designing a better model, it’s worth understanding what’s broken.
1. Siloed Tools and Data
Security tools operate independently:
- Vulnerability scanners
- Endpoint protection
- Cloud security tools
- Identity systems
Each provides partial insight. None provide the full picture.
2. Lack of Business Context
Most tools tell you what is wrong, but not what matters.
A critical vulnerability on a low-impact system may not be urgent.
A medium-risk issue on a revenue-critical system might be.
Without context, prioritization becomes guesswork.
3. Alert Fatigue
Security teams are overwhelmed with alerts.
- Too many signals
- Not enough clarity
- Limited ability to act
This leads to missed risks and delayed responses.
4. Compliance Over Security
Many organizations optimize for audits instead of actual risk reduction.
They check boxes instead of asking:
“Are we truly secure?”
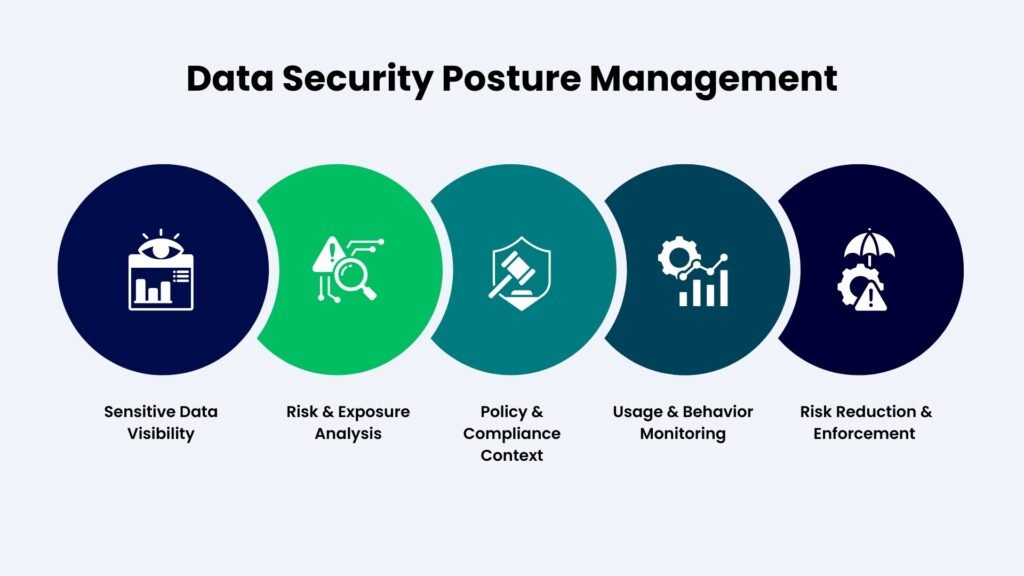
The Shift: From Risk Management to Risk Posture Management
The difference is subtle but important.
Risk Management focuses on processes and controls.
Risk Posture Management focuses on outcomes and visibility.
It brings together:
- Security signals
- Asset context
- Threat intelligence
- Business impact
Into a unified view.
The Unified Model for IT Risk Posture Management
Let’s break this into a practical framework you can apply.
1. Asset Visibility: Know What You Have
You cannot manage risk without knowing your assets.
This includes:
- Cloud infrastructure
- SaaS applications
- Endpoints
- APIs
- Data stores
Actionable Approach
- Build a centralized asset inventory
- Use automated discovery tools
- Continuously update asset ownership and classification
Key Insight
Most organizations underestimate how many assets they actually have. Hidden assets often carry the highest risk.
2. Contextual Risk Scoring: Prioritize What Matters
Not all risks are equal.
A unified model assigns risk based on:
- Severity of the vulnerability
- Exposure level (public vs internal)
- Business criticality
- Data sensitivity
- Exploit likelihood
Example
Two systems have the same vulnerability:
- System A: Internal HR tool
- System B: Public-facing payment API
System B should be prioritized.
What to Implement
- Risk scoring models that combine technical and business data
- Dynamic prioritization instead of static severity levels
3. Continuous Monitoring: Stay Updated in Real Time
Risk posture changes constantly.
You need:
- Real-time alerts
- Continuous scanning
- Automated updates
Why This Matters
A vulnerability introduced today should not wait for next month’s scan.
4. Threat Intelligence Integration
Understanding vulnerabilities is not enough. You need to know:
- Are they being actively exploited?
- Are they relevant to your industry?
Actionable Strategy
Integrate threat intelligence feeds to:
- Identify active threats
- Prioritize based on real-world risk
- Reduce noise
5. Unified Dashboard: One Source of Truth
This is where everything comes together.
A strong IT Risk Posture Management system provides:
- A centralized risk view
- Trends over time
- Drill-down capabilities
- Clear prioritization
What Leadership Needs
- A simple risk score
- Clear top risks
- Actionable recommendations
6. Automated Remediation Workflows
Identifying risk is only half the job.
You need to fix it efficiently.
Examples
- Auto-patching vulnerabilities
- Triggering configuration fixes
- Assigning tasks to owners
- Tracking remediation progress
Key Insight
Speed of remediation is as important as detection.
7. Feedback Loops and Continuous Improvement
Your model should evolve.
Track:
- Time to detect
- Time to remediate
- Recurring issues
- Risk reduction trends
Use this data to improve processes.
Mini Case Example: From Chaos to Clarity
A mid-sized SaaS company struggled with fragmented security tools.
Problems included:
- Duplicate alerts
- Poor prioritization
- Slow response times
They implemented a unified IT Risk Posture Management approach:
- Centralized asset inventory
- Integrated security tools
- Built contextual risk scoring
- Created a unified dashboard
Results
- 40% reduction in alert noise
- Faster remediation cycles
- Clear visibility for leadership
- Improved audit readiness
The biggest change was not technical. It was clarity.
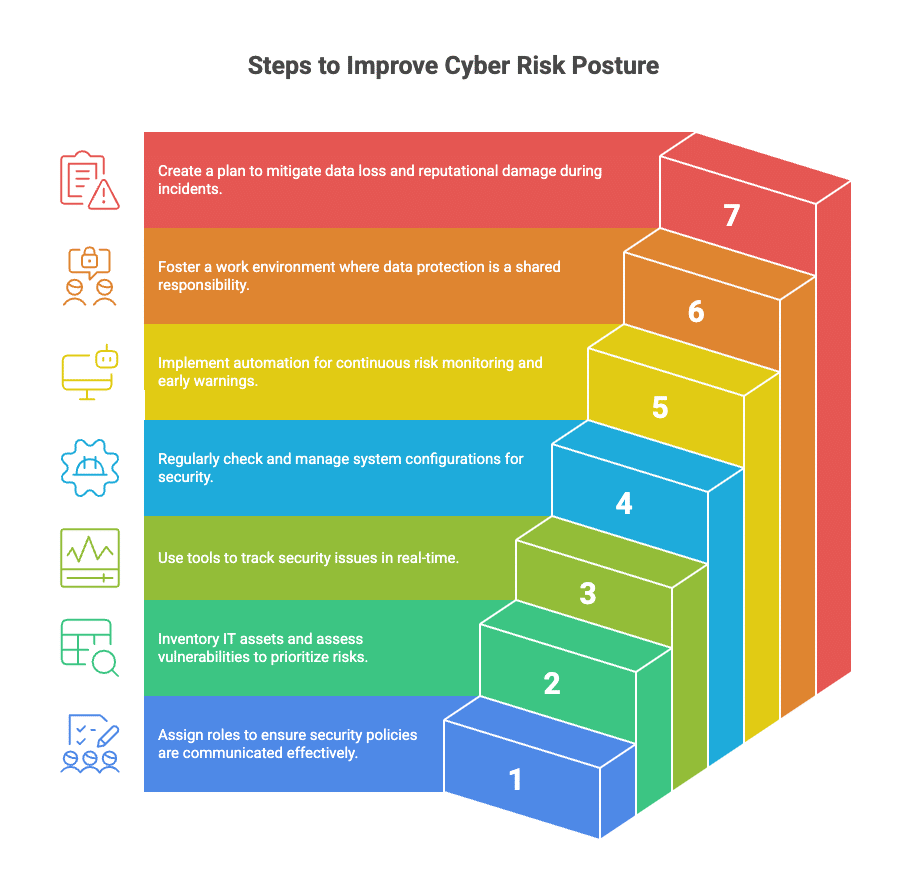
Practical Framework: How to Get Started
You don’t need to overhaul everything at once.
Step 1: Audit Your Current State
Ask:
- What tools are we using?
- What data do they generate?
- Where are the gaps?
Step 2: Centralize Data
Bring data into a common platform or data layer.
Avoid tool sprawl without integration.
Step 3: Define Risk Criteria
Align with business stakeholders:
- What systems are critical?
- What data is sensitive?
- What risks are unacceptable?
Step 4: Implement Scoring and Prioritization
Move beyond CVSS scores.
Incorporate business context.
Step 5: Build Visibility
Create dashboards for:
- Security teams
- IT teams
- Leadership
Step 6: Automate Where Possible
Start with:
- High-frequency tasks
- Low-risk remediation
- Alert triage
Step 7: Measure and Improve
Track progress and refine your model.
Common Mistakes to Avoid
1. Over-Reliance on Tools
Tools are enablers, not solutions.
Without a clear model, more tools add complexity.
2. Ignoring Business Context
Security decisions must align with business priorities.
Otherwise, you fix the wrong problems.
3. Trying to Fix Everything at Once
Prioritization is key.
Focus on high-impact risks first.
4. Lack of Ownership
Every risk should have a clear owner.
Without accountability, nothing gets resolved.
A Contrarian Take: More Data Is Not the Answer
Many organizations believe that collecting more data will solve their risk problems.
It won’t.
The real challenge is not lack of data. It’s lack of clarity.
- Too many signals
- Too little insight
- Too many dashboards
- Too few decisions
A unified IT Risk Posture Management model is about simplifying, not complicating.
Quick Checklist: Is Your Risk Posture Management Effective?
Use this as a quick self-assessment:
- Do you have a complete and updated asset inventory?
- Can you prioritize risks based on business impact?
- Do you have real-time visibility into your environment?
- Are your security tools integrated?
- Can leadership understand your risk posture easily?
- Are remediation processes fast and measurable?
If you answered “no” to several of these, there’s a clear opportunity to improve.
The Future of IT Risk Posture Management
As enterprises grow more complex, this discipline will become central to operations.
Expect to see:
- AI-driven risk prioritization
- Predictive risk modeling
- Deeper integration across tools
- Real-time decision support
Organizations that adopt unified models early will have a clear advantage.
They will not just react to risk. They will anticipate and manage it proactively.
Conclusion: From Visibility to Control
IT risk is not going away. If anything, it’s accelerating.
The question is not whether you have risk. It’s whether you understand it.
A unified IT Risk Posture Management approach gives you:
- Clear visibility
- Better prioritization
- Faster response
- Stronger alignment with business goals
Start small. Focus on visibility and prioritization first.
Then build toward automation and continuous improvement.
Because in modern enterprises, the ability to understand and manage risk is no longer optional. It’s a core capability that defines resilience and long-term success.







Leave a Reply